The most important aspect of security awareness training is making it role-specific. Generic modules don’t work. I’ve watched organizations burn through budgets on annual slide decks that employees click through in 20 minutes and forget by lunch. Roughly 95% of data breaches involve human error (Mordor Intelligence, 2026), and the security awareness training market hit $5.77 billion in 2025 because companies finally realized people are the weakest link.
Security awareness training is a structured program that teaches employees how to recognize, avoid, and report cyber threats specific to their job. Effective programs go beyond compliance checkboxes by using phishing simulations, micro-learning sessions, and role-based content tailored to each department’s risk profile. When done right, organizations see phishing-prone rates drop from 34.3% to 4.6% within a year (Mordor Intelligence, 2026).
This article won’t cover vendor comparisons or platform reviews. It focuses on what makes training actually work, how to measure it, and where most companies get it wrong.
What Does Role-Based Security Awareness Training Mean?
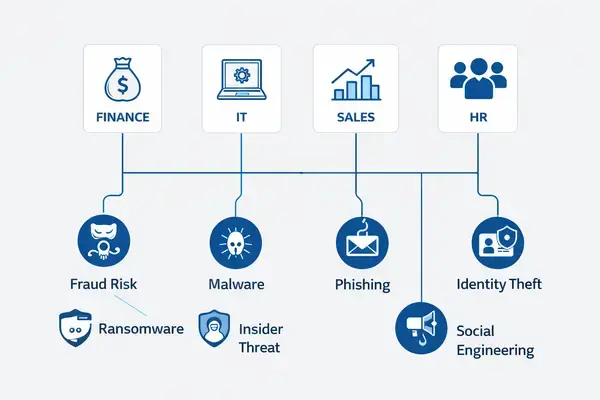
Role-based security awareness training matches the lesson to the job. Your finance team doesn’t face the same threats as your marketing team, so why would they sit through the same course?
Here’s what this looks like in practice. Finance staff get focused training on invoice fraud and business email compromise. IT teams train on access controls and credential hygiene. Sales teams learn to spot social engineering during client interactions. HR staff study resume-based malware and fake applicant profiles.
One in three employees say their training doesn’t apply to their daily work. That stat alone should make you rethink your program. When the content connects to what someone actually does every day, they pay attention. And when they pay attention, they remember. Cloud-based training platforms now hold roughly 73% of the market because they make this kind of targeting possible at scale.

The Real Reason Role-Based Training Outperforms Generic Programs
Most companies treat security awareness like a compliance task. Check the box, move on. But that misses the point entirely.
When employees see how an attack would target their specific role, something clicks. It stops being abstract. A procurement manager who understands vendor email compromise is a different employee than one who sat through a generic “don’t click suspicious links” video. The Bureau of Labor Statistics projects information security analyst roles to grow 29% from 2024 to 2034. That talent gap isn’t closing. Your existing staff carries more of the security burden, whether they signed up for it or not.
Role-specific programs also create distributed checkpoints. Instead of one IT team watching everything, every department becomes a sensor. Threats that slip through a single-layer defense get caught because people know what “wrong” looks like in their context. That’s how trained security-minded professionals actually prevent incidents.
How Do You Measure Whether Security Awareness Training Is Working?
You can’t improve what you don’t measure. And completion rates don’t count. Someone finishing a course doesn’t mean they’ll report a suspicious email on Tuesday.
According to IBM’s 2025 Cost of a Data Breach Report, the global average breach cost sits at $4.44 million. Phishing-specific breaches run closer to $4.8 million. In the U.S., that number climbs to around $10.22 million. Those figures put a hard dollar amount on why measurement matters. Organizations with high-frequency, year-long training programs saw phishing-prone rates crash from 34.3% to 4.6% (Mordor Intelligence, 2026).
Phishing Simulation Metrics That Actually Matter
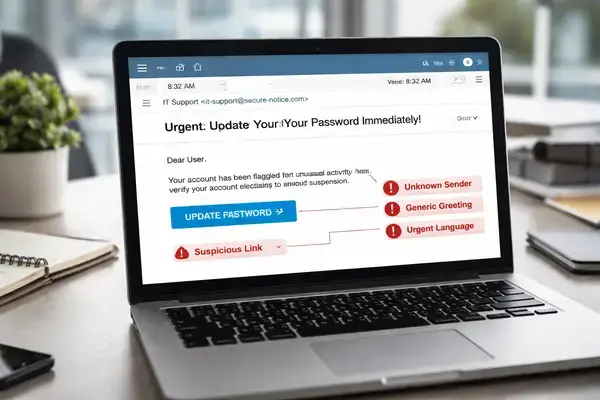
Phishing simulations are the closest thing you’ve got to a real-world test. But most companies only track click rates, and that’s a mistake.
Track these instead: click rates by department, time between receiving and reporting a suspicious message, performance trends over multiple quarters, and success rates against advanced attacks. The gap between “I saw it” and “I reported it” matters more than whether someone clicked. For businesses investing in security improvements, these metrics prove real-world value.
What Incident Reports Reveal About Your Training Gaps
Daily operations tell you more than any test score. Track the number and quality of security incident reports, false positive rates, staff participation in voluntary security conversations, and time to detect suspicious activity.
Here’s the contrarian take: a spike in reported incidents after new training isn’t a bad sign. It usually means awareness went up. People are catching things they used to ignore. The goal isn’t zero reports. It’s smarter, faster reporting. If your staff stops reporting because they’re afraid of looking foolish, your program just became counterproductive.
AI-Powered Threats Changed the Rules in 2026
Attackers now use AI to build phishing emails that sound exactly like your CEO. These aren’t the broken-English scam messages from 2015. Generative AI tools scrape LinkedIn profiles, mimic writing styles, and time messages to match legitimate business workflows.
The SANS Institute’s 2025 Security Awareness Report (surveying 2,700+ professionals across 70 countries) stressed that programs need to move beyond compliance toward measurable behavior change. Old-school annual training can’t keep pace with threats that evolve weekly. Micro-learning sessions of about 15 minutes, delivered quarterly, combined with monthly simulations, consistently outperform annual sessions. That’s not opinion. That’s what the data across multiple studies keeps showing. Cyber insurance carriers now routinely demand proof of quarterly simulations before offering premium discounts up to 20%.
Building a Security Awareness Program That Doesn’t Go Stale
The biggest mistake I see? Companies launch a training program and treat it like a finished product. Security awareness isn’t a project with a completion date. It’s an ongoing process.
Start with role-based content mapped to actual job functions. Layer in phishing simulations that get harder over time. Update modules whenever a new threat pattern emerges. Track behavioral changes, not just completion rates. Feed the results back into training design.
Budget-wise, expect to pay $12 to $36 per employee per year for a solid platform that includes simulations and reporting. Mid-range options ($20–36) cover most needs. The market average sits around $38.72 per user annually (Mordor Intelligence, 2026). Compare that to a single breach costing $4.44 million on the low end, and the math isn’t close. Organizations working with a team that understands their industry can also improve how they communicate training value internally to leadership and insurers.
New regulatory pressure makes this harder to ignore. Over 800 state-level cybersecurity bills were introduced in 2025 (NCSL). CMMC finalized in September 2025. Waiting isn’t a strategy. Building a training program now, with the right security personnel supporting it, gives your organization a measurable advantage.
FAQs
How often should employees receive security awareness training?
Quarterly micro-learning sessions (about 15 minutes each) combined with monthly or quarterly phishing simulations consistently outperform annual training. Organizations using this frequency saw phishing-prone rates drop from 34.3% to 4.6% within 12 months (Mordor Intelligence, 2026). Annual sessions are the bare minimum for compliance, but they don’t change behavior.
Is security awareness training actually effective or just a checkbox?
It depends entirely on how it’s delivered. Programs that include phishing simulations and role-based content reduce human-driven incidents by 50% to 86%. SMBs with strong programs save an average of $5.4 million in breach-related losses. But generic annual courses without simulations fail almost every time.
What does security awareness training cost per employee?
The market average is roughly $38.72 per user per year (Mordor Intelligence, 2026). Budget platforms start around $12 to $20 per user. Mid-range options with simulations and reporting run $20 to $36. High-end platforms with AI personalization cost $36 to $50+. Compare any of those to a single breach averaging $4.44 million globally.
Does security awareness training protect against AI-generated phishing?
Yes, but only if the training stays current. Programs updated for 2026 threats (including deepfake voice and AI-written emails) paired with frequent simulations give employees the pattern recognition they need. Older annual programs built around 2020-era threats leave significant gaps.
How do you prove security awareness training ROI to leadership?
Track three things: phishing simulation click rates over time, incident reporting speed, and breach avoidance savings. Many cyber insurance carriers now offer premium discounts up to 20% for organizations that provide quarterly simulation proof. Those savings alone can offset the entire training budget.
Do small businesses need security awareness training if they have antivirus?
Absolutely. Antivirus catches known malware. It doesn’t stop an employee from wiring $50,000 to a spoofed vendor account. Since 95% of breaches involve human error, technical controls alone aren’t enough. Even basic programs costing $12 per user per year significantly reduce risk for small businesses.
Can employers discipline workers for failing phishing simulations?
Most security professionals advise against it. Using simulation failures as grounds for discipline creates a fear-based culture where employees stop reporting suspicious activity. The goal of simulations is education, not punishment. Companies that punish failures typically see reporting rates decline, which leaves the organization more exposed.



